Have you been hooked by a phishing email?
Phishing scams are one of the most common ways hackers gain access to sensitive or confidential information. In fact, according to the Verizon’s 2018 Data Breach Investigations Report, phishing is involved in 70 percent of breaches that feature a social engineering component.
Discover the Top 5 Remote Security Threats to your workforce with our free whitepaper
What is Phishing?
At the most basic level, a phishing scam involves sending fraudulent emails that appear to be from a reputable company, with the goal of deceiving recipients into either clicking on a malicious link or downloading an infected attachment, usually to steal financial or confidential information.
If your employees don’t know the signs of a phishing email, your company is at risk. According to Verizon, the average time it took for the first victim of a large-scale phishing campaign to click on a malicious email was 16 minutes; however, it took twice as long — 33 minutes — for a user to report the phishing campaign to IT.
Given that 49 percent of malware is installed via email, these 17 minutes could spell disaster for your company.
How to Spot a Phishing Scam
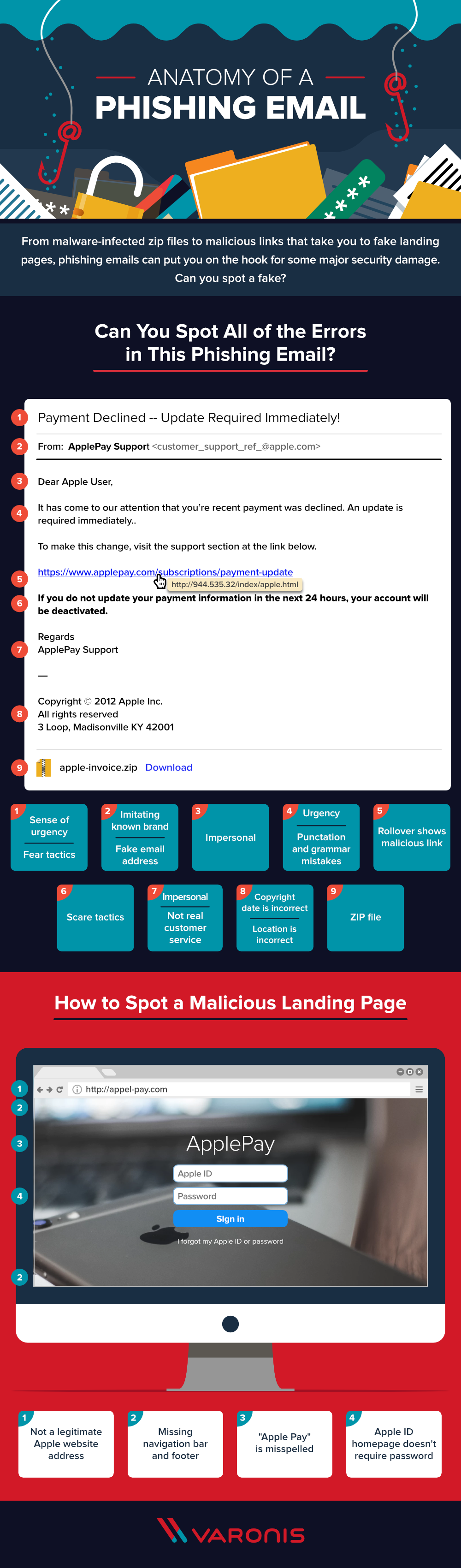
We’ve broken out the most common components of a phishing email. Check out our full infographic to test your knowledge.
How many did you get? Read on to learn more about the identifying characteristics of a typical phishing email.
Subject line
Phishing campaigns typically aim to create a sense of urgency using intense language and scare tactics, starting with the email’s subject line. Common themes among phishing emails are that something sensitive, such as a credit card number or an account, has been compromised. This is done to induce the recipient into responding quickly, without recognizing the signs of a scam.
“From” field
To work, phishing campaigns must trick the email recipient into believing that the message is from a reputable company. As such, the email will appear to come from a legitimate entity within a recognized company, such as customer support. Upon closer look, however, you can see that both the name of the sender and the sender’s email address is a spoof on a known brand, not a real vendor.
“To” field
Phishing emails are often impersonal, addressing the recipient as a “user” or “customer.” This is a red flag; while businesses may send out mass eblasts announcing a sale or service, legitimate companies will address you by name when asking for an update to financial information, or dealing with a similarly sensitive matter.
Body copy
As with the subject line, the body copy of a phishing email is typically employs urgent language designed to encourage the reader to act without thinking. Phishing emails are also often riddled with both grammar and punctuation mistakes.
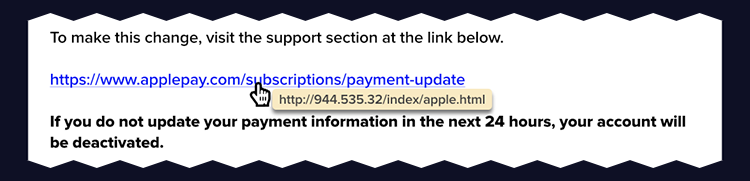
Malicious link
A suspicious link is one of the main giveaways of a phishing email. These links are often shortened (through bit.ly or a similar service) or, as above, are formatted to look like a legitimate link that corresponds with the company and message of the fake email. However, rolling over the link shows a malicious address that doesn’t take you to the stated web address.
Scare tactics
In addition to urgent language, phishing emails often employ scare tactics in hopes that readers will click malicious links out of alarm or confusion. Such messaging is often framed around updates that are immediately required or payments that must be made within a certain amount of time.
Email sign-off
As with the email’s greeting, the sign-off is often impersonal — typically a generic customer service title, rather than a person’s name and corresponding contact information.
Footer
A phishing email’s footer often includes tell-tale signs of a fake, including an incorrect copyright date or a location that doesn’t correspond with that of the company.
Attachment(s)
In addition to malicious links, phishing scams often include malicious downloadable files, often compressed .zip files, which can infect your computer.
Malicious landing page
If you do click on a phishing link, you’ll often be taken to a malicious landing page, much like the one above. There are several ways to spot a malicious landing page:
- Website address: The web address of a malicious landing page attempts to mimic the web address of a legitimate company, but errors such as misspellings and unsecure connections denote an unsafe website.
- Missing navigation and footer: The goal of a malicious landing site is to take your information. As such, these pages are often bare-bones. Here, you can see that the landing page is missing both the header and footer of Apple’s ID sign-in page.
- Misspelling: Like in the phishing email, the malicious landing page will attempt to mimic a real company, but small oversights can tip you off: like above, where “Apple Pay” is misspelled as one word.
- Information collection: The goal of phishing scams is to get you to enter personal or financial information, so malicious landing pages will almost always include some type of information collection form that deviates slightly from the company’s legitimate landing page. In the malicious page above, users are required to enter their Apple ID password; this is not required on the actual Apple ID login page.
So, were you able to spot all the errors? As phishing attacks become more common — and phishing tactics more sophisticated — it’s important to inspect all unsolicited emails with a careful eye.
Email recipients don’t shoulder all the burden, however. To truly combat phishing tactics, companies must become more vigilant, through both employee training and the use of security software, to better spot and prevent potentially debilitating attacks.
What you should do now
Below are three ways we can help you begin your journey to reducing data risk at your company:
- Schedule a demo session with us, where we can show you around, answer your questions, and help you see if Varonis is right for you.
- Download our free report and learn the risks associated with SaaS data exposure.
- Share this blog post with someone you know who'd enjoy reading it. Share it with them via email, LinkedIn, Reddit, or Facebook.